Solid Data Security
helps organizations achieve:

Highly mature and responsive governance processes
Greater efficiency and reduced redundancy of effort
Increased awareness of security attacks and potential breaches

How We Approach
Data Security
Review policies and requirements to formulate coherent security strategies
Perform system-wide reviews of business processes and strategic decision-making
Analyze platforms, tools, and architectures to ensure that systems are both compliant and truly secure
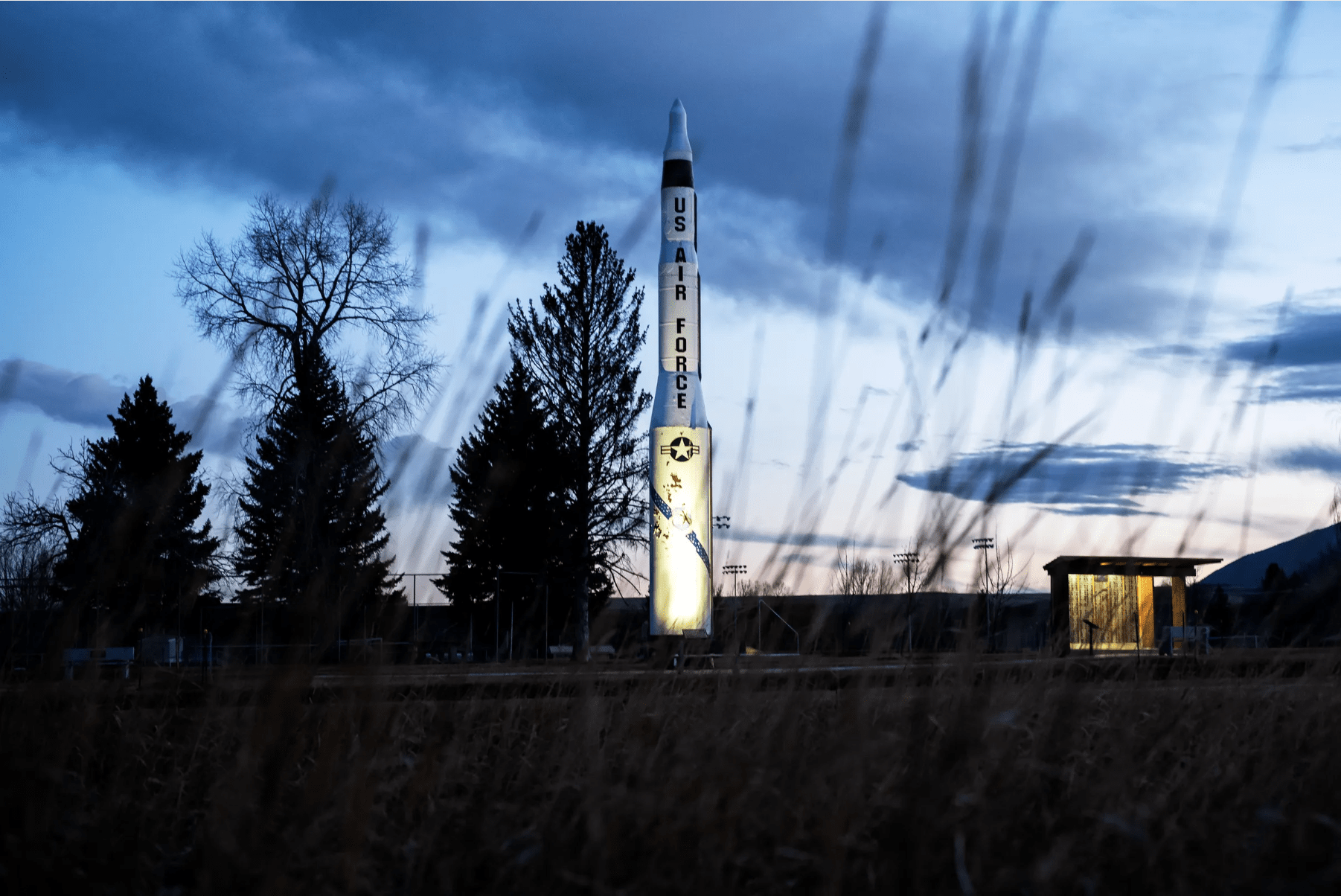
Data Security Success Stories
Your Team of Experts in Data Security
-
Regulations (e.g., CMS and ONC rules, HIPAA, ITAR, and HEDIS)
-
Plans of Action and Milestones (POA&M)
-
Security Incident and Event Managers (SIEMs)
-
Risk Management Frameworks (e.g., NIST)
-
Authority to Operate (ATO) processes

Technologies We Utilize
Discover. Transform. Integrate.
Beyond Data Security Solutions
Want to Join a Growing Team of Data Experts?
Join a team that believes in the power
of collaboration and teamwork.

Resources on
Data Management
White Paper on Microelectronics Supply Chain Security
White Paper on Microelectronics Supply Chain Security
White Paper on Semiconductor Device Security
White Paper on Semiconductor Device Security